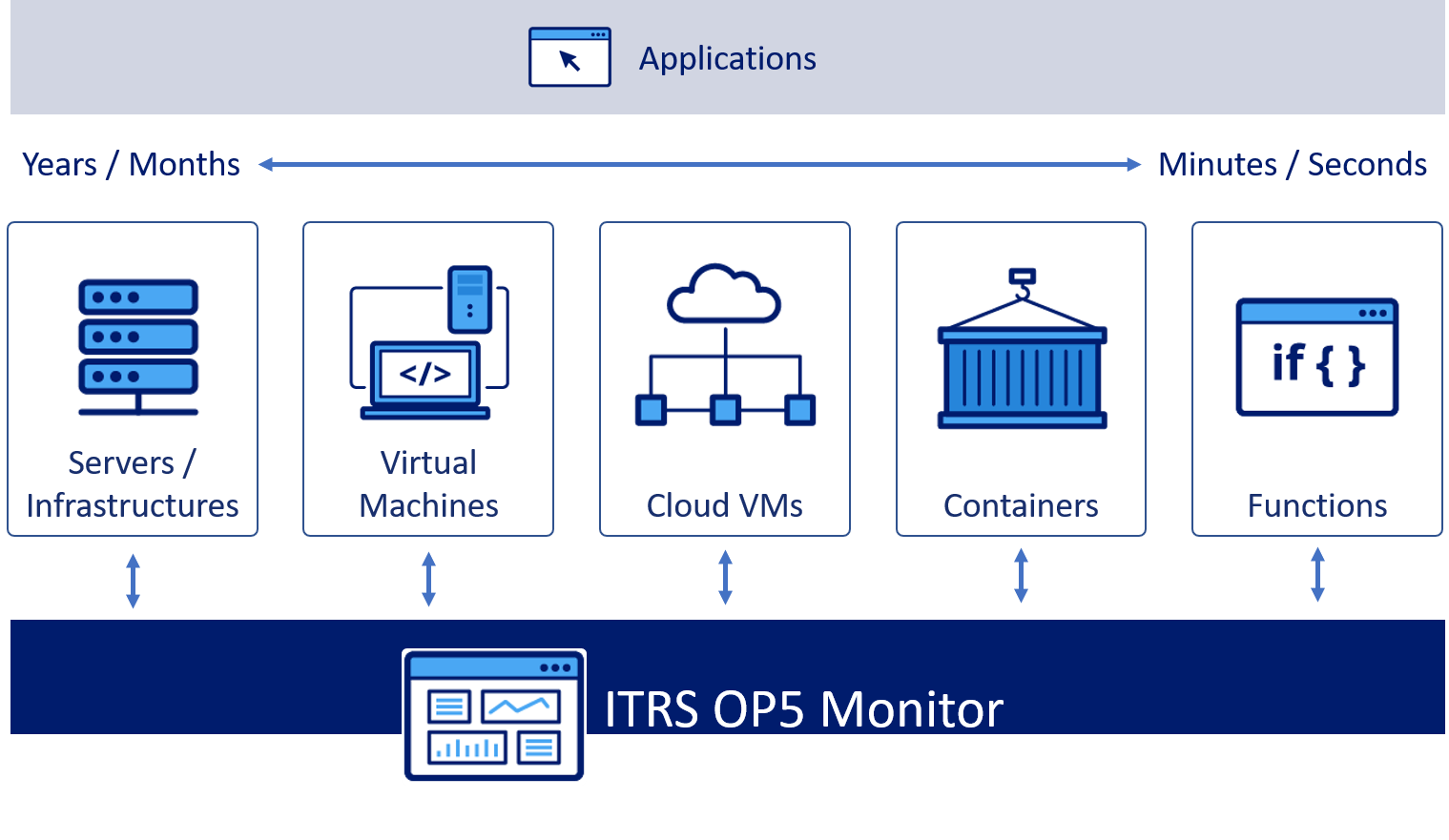
Many of our customers have started to incorporate cloud into their IT estate. This is a natural evolution, and OP5 Monitor shall continue to be a best-in-class monitoring tool for networks and on-premise environments, while evolving to support dynamic environments. We call the mix between traditional IT and dynamic environments the Hybrid IT. We have already started the work of supporting Hybrid IT environments with these new items:
- We have created the Slim Poller, a containerised lightweight version of OP5 Monitor poller configuration. This was especially designed to enable the OP5 Monitor poller to run as a container in environments such as OpenShift and Kubernetes. Slim Poller supports autoscaling in Kubernetes, can be set up automatically with environment variables, and can auto-register with the cluster.
- We have created a plugin specifically for monitoring Amazon Web Services (AWS) resources. The plugin allows for this by accessing the AWS native cloud monitoring called CloudWatch.
- We have created a plugin for monitoring of Kubernetes cluster components such as deployments (replicas), nodes, and pods.
- We have the latest version of OP5 Monitor available in AWS and Azure Marketplace for easy deployment in the cloud.
- The
check_vmware_v2plugin replaces thecheck_vmware_apiplugin to bring extended capabilities for monitoring VMware networks.