Roles
Overview Copied
The configuration, addition and deletion of Roles is done via the Users and Roles section of the Configuration menu. Once within Users and Roles, click on the Roles tab:
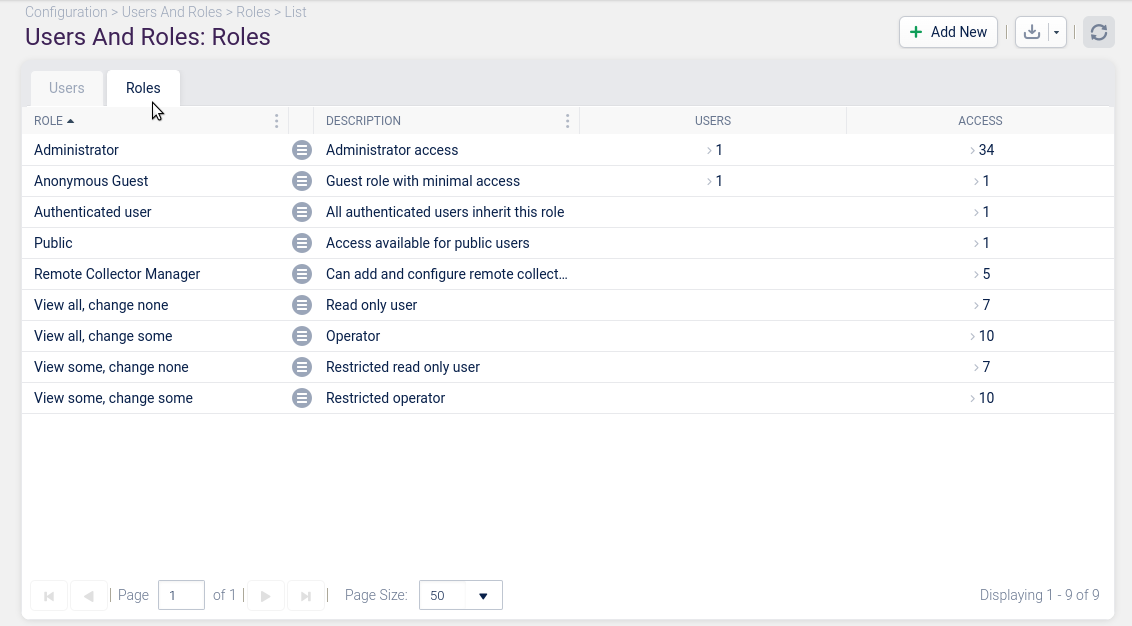
In this view, you can choose to:
- add a new Role using the Add New button.
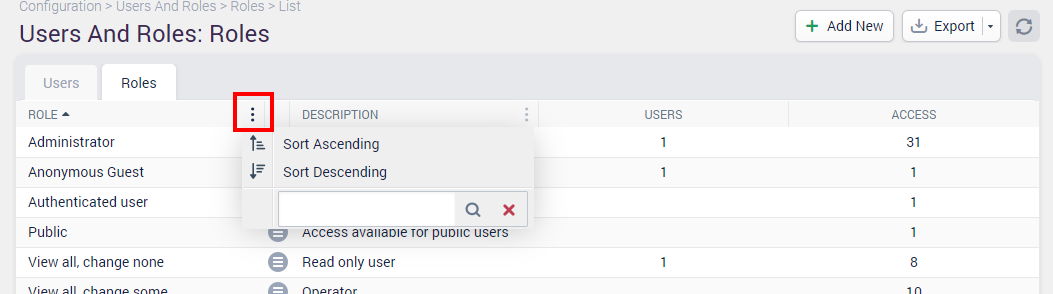
- to edit or delete a Role using the contextual menu.
- export the list of Roles via the Export button.
- filter the list of Roles using the filters within the column headers.
Adding a Role Copied
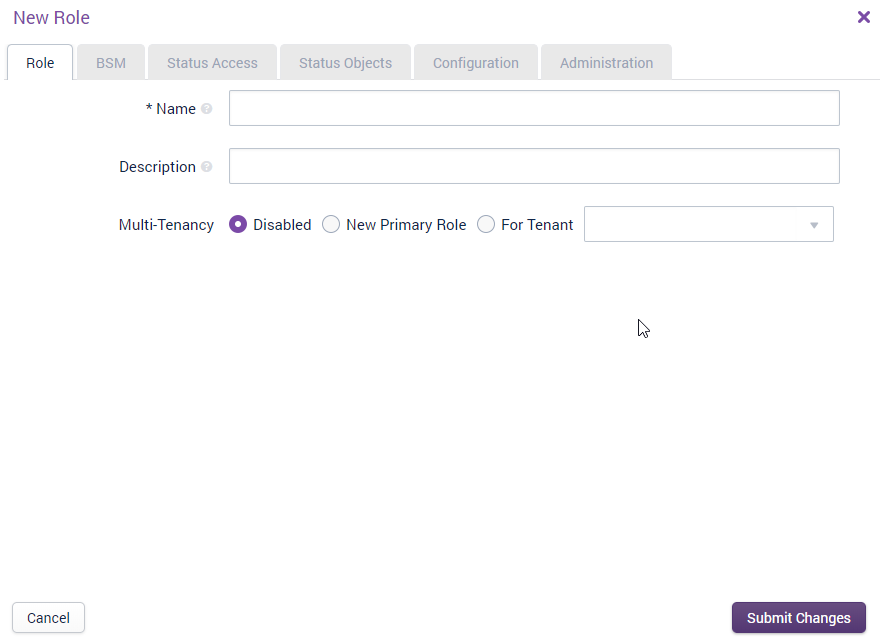
To add a new Role, click on the Add New button.
The New Role configuration window is displayed:
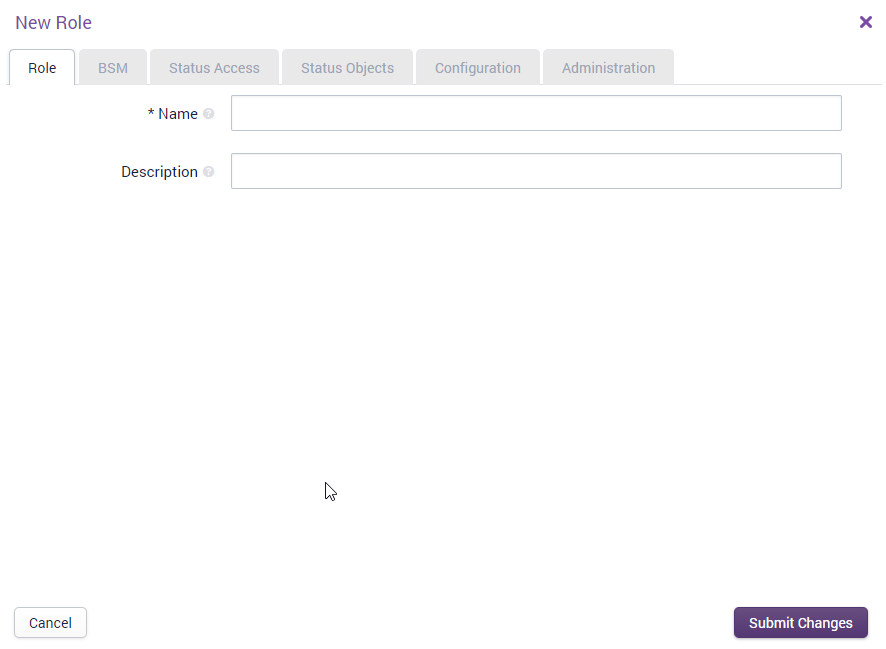
There are six tabs within the ‘New Role’ window:
Role tab Copied
Assigns a name and description to the Role. If Multi-tenancy is enabled, it will be displayed here.
BSM tab Copied
Defines the access control and visibility for Business Service Monitoring, i.e. can users within this Role add Business Services or Components, and also which Business Services can they see when logged in.
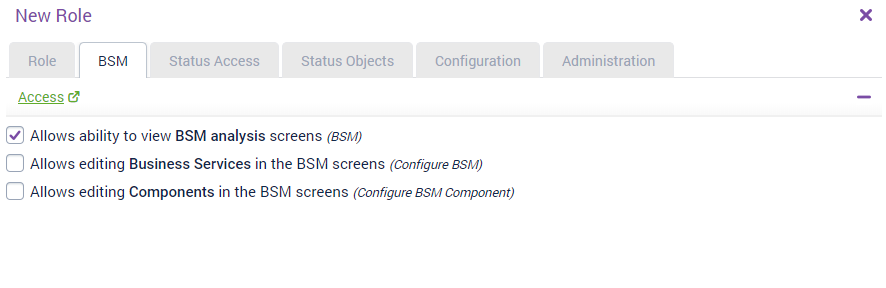
If the ‘Allows ability to view BSM analysis screens (BSM)’ checkbox is not checked, then the rest of the options will be hidden.
Authorised for Business Services
This section is where you can determine which Business Services the user can view (via dashboards), and which ones they can both view and edit. In our example, we are not going to configure any access for editing and viewing BSM items.
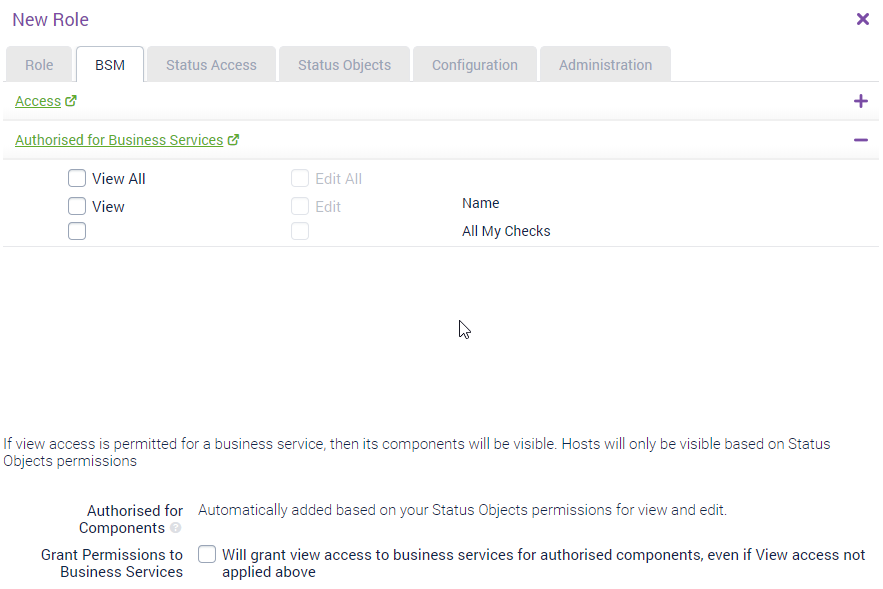
You can control which Business Services are available for a Role from a ’top down’ or from a ‘bottom up’ approach.
Top Down
Choose the specific business service in the Authorised for Business Services field. If you select View All, then all Business Services will be available including any new Business Services created in the future. Access to the Business Service will allow visibility of all components of the Business Service.
Bottom Up
Components will be automatically selected based on your existing status object permissions (based on Host Group / Service Group intersection or Hashtags). The ‘intersection’ is explained in detail within the ‘Status Objects’ tab.
Permissions for components are automatically granted based on the existing status object definitions. If VIEWALL is specified, then all components are visible. Otherwise, it is based on the Host Group/Service Group intersection and Hashtags. You need to see all hosts for the component to be visible.
If the component consists of 20 Service Checks, then the user will need to have permission to all 20 Service Checks in order for the component to be visible.
If you select the ‘Grant permissions to Business Services’ checkbox, then the Business Services associated with all your components will be visible.
Status Access Copied
Defines what users assigned this Role can do within Opsview Cloud when logged in; e.g. can they view dashboards, create dashboards, and send notifications.
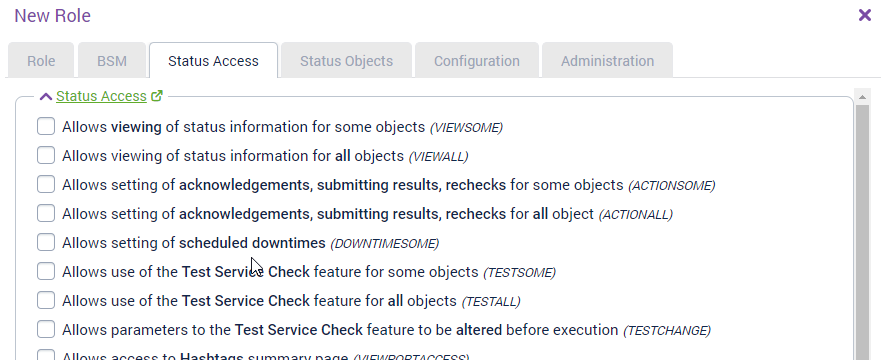
Within this tab you can configure what access rights users of this Role have, for example can they create and edit dashboards, view Flow data, send notifications, and so on.
In this tab, we need to check VIEWSOME (‘Allows viewing of status information for some objects’), where ‘some objects’ are the items they are allowed to view as per the Status Objects tab.
We should also check, NAVOPTIONS, RRDGRAPHS, TESTSOME, DOWNTIMESOME, and ACTIONSOME.
Status Objects Copied
Defines which objects the users within this Role can see, including Host Groups, Service Groups, and Hashtags.
Within the Status Objects tab, you can select which Host Groups or Service Groups a role can access. For example, if you want to allow access only to Database Servers, select that host group from the left-hand column and click Add To Selected.


To remove an item, select that item from the right-hand column and click Remove From Selected.

The Search function allows you to find specific items quickly from the list of Host Groups, Service Groups, or Hashtags.
Alternatively, we can tag those Hosts and Service Checks with a Hashtag, for example opsview-servers, and then select that within Authorised for Hashtags.
Configuration Copied
Defines which objects and sections the users within this Role can configure, e.g. can they access the Hashtags section of the Configuration menu.

Within the Configuration tab, you can define the Host Groups that users can edit (and thus the hosts within). You can also define other items users can configure within the monitoring software, i.e. can they edit the hosts they have access to view, can they edit other users, and so forth.
The Monitoring Clusters section defines which Monitoring Clusters (and Monitoring Collectors) will be visible for the role when making configuration changes.
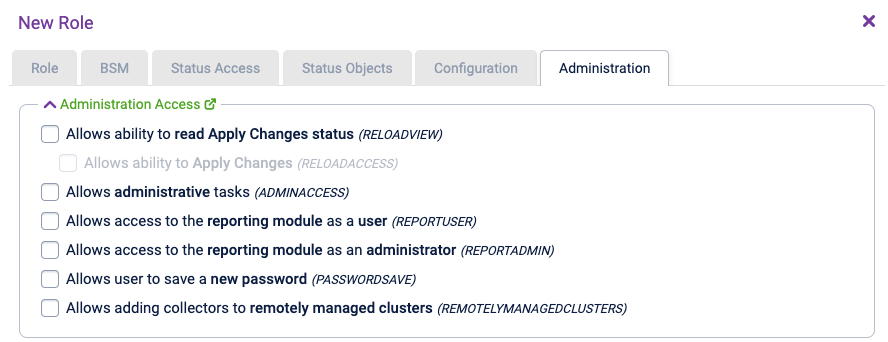
Administration Copied
The administrative permissions are defined within this tab, and determine if users within this Role can Apply global save new passwords or view reporting.
Once you have configured the above six tabs, click ‘Submit Changes’ and your new Role will be created:
We can now apply this new Role to a test user, as below:
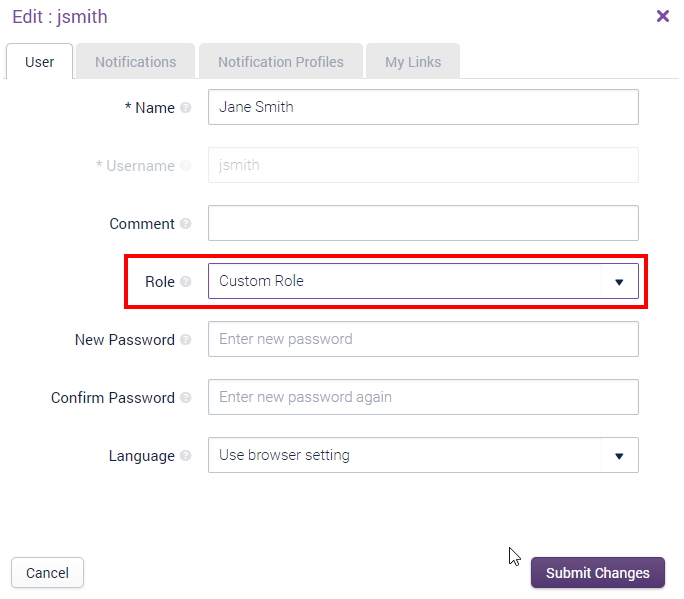
The Role is set to ‘Opsview Servers’. After saving the new user and completing an Apply Changes (from the Configuration menu), you can now log in with the new user and see that the permissions have been correctly applied.
Current role definitions Copied
Key
- (AC) — if you make changes to a role, you must Apply Changes via the Configuration menu before the changes take effect.
- (AO) — the administrator should be the only person with this permission, as Opsview needs to list every item for configuration.
These are the access levels:
- VIEWALL — view all (AC). This will also include all Business Services and Business Components.
- VIEWSOME — view some (AC) - see below for the definition of some.
- ACTIONALL — action all (AC).
- ACTIONSOME — action some (AC) - see below for the definition of some.
- Action ability includes: setting acknowledgments, editing the built-in wiki. Setting downtime requires
DOWNTIMESOME.
- Action ability includes: setting acknowledgments, editing the built-in wiki. Setting downtime requires
- DOWNTIMESOME — set downtime for their list of objects. See below for the definition of some (AC).
- TESTALL — run the Test Service Check function.
- TESTSOME — as
TESTALL, but see below for the definition of some. - TESTCHANGE — run the Test Service Check function and have the ability to change the arguments for troubleshooting.
- DASHBOARD — allow access to the dashboard.
- DASHBOARDEDIT — allow the user to make private changes to their dashboard.
- VIEWPORTACCESS — viewport access.
- RRDGRAPHS — RRD graphs.
- If RRD graphs are set to public, then
/graphand/rrdgraphwill be available to non-logged in users. They will also be allowed to view all hosts and all services. - If RRD graphs are set to authenticated users, then the hosts and services allowed to be accessed will be restricted to the subset of the host group and service group intersection.
- If RRD graphs are set to public, then
- NOTIFYSOME — notify some (AC) - see below for the definition of some.
- AUTODISCOVERY — use the Autodiscovery application.
- AUTOMONITOR — use the Automonitor application. Other permissions will be required.
- CONFIGUREHOSTS — view configuration for hosts.
- You choose which points in the Host group hierarchy this role has, which means only hosts within those host groups are allowed to be configured. To be able to configure all hosts, select the top level host group.
- If you select any monitoring servers, you are only allowed to mark hosts against these particular monitoring servers.
- CONFIGUREKEYWORDS — view configuration for Hashtags (formerly called Keywords). A user with this access would be able to get a list of all Service Checks, Hosts, and Contacts for the system.
- CONFIGUREPROFILES — view configuration for shared notification profiles for their role. If the user also has
ADMINACCESS, they can see profiles for all roles (AO). - CONFIGUREHOSTGROUPS
- CONFIGURECONTACTS
- CONFIGUREROLES (AO)
- CONFIGURETENANCIES
- CONFIGURENETFLOW — configure NetFlow.
- CONFIGUREVIEW — view configuration of everything else that does not have its own access point above. As new access points are created, less will be covered by
CONFIGUREVIEW. - CONFIGUREREMOTECLUSTER — add new remotely managed clusters from the Configuration > Collector Management page. This must also have
CONFIGUREVIEWpermission. - CONFIGURESAVE — save configuration changes. Removing this access effectively gives a view only ability to look at the configuration data (some passwords will be visible).
- RELOADVIEW — displays the number of changes badge in the navigation bar and can open the Apply Changes window from the Configuration menu.
- RELOADACCESS — can start the Apply Changes process from the Apply Changes window to put the latest configuration into production.
- ADMINACCESS — admin access, including audit log access.
- REPORTUSER — access to Opsview Reporting Module.
- REPORTADMIN — allow administrator access in Opsview Reporting Module.
- NETFLOW — ability to view the NetFlow dashlets.
- PASSWORDSAVE — ability to change their own password.
- REMOTELYMANAGEDCLUSTERS — add collectors to remotely managed clusters.
Users may need to refresh their web page in the browser for their permissions to take effect.
Note
ADMINACCESSdoes not allow access to everything. Currently, it is used for administrator access, but as more granular access points are added, the items withinADMINACCESSwill decrease (but upgrade scripts will ensure that new access points are split appropriately).
On initial systems, these roles will exist:
Public Copied
Note
Only RRD graphs and Viewport access make sense to be public)
- Viewport access
Authenticated User Copied
- RRD graphs
Admin role Copied
- View all
- Action all
- Notify some
- Admin access
- Configure hosts
- Configure view
- Configure save
- Apply Changes access (reload)
Remote Collector Manager Copied
- Configure hosts
- Configure host groups
- Configure view
- Configure save
- Remotely managed clusters
View all, change some Copied
- View all
- Action some
- Notify some
View some, change some Copied
- View some
- Action some
- Notify some
View all, change none Copied
- View all
- Notify some
View some, change none Copied
- View some
- Notify some
Selection of objects Copied
For access levels which refer to some, this is the selection of objects based on the role.
The selection consists of the union of the following:
- Intersection of the Authorised for Host Groups and Authorised for Service Groups tick boxes, so only services from the specified service groups that exist on a host from the specified host groups will be included in the subset.
- List of authorized keywords.
This allows you to ‘slice’ the services that you can see on a host.
We recommend that you use service groups to match your team function or areas of responsibility (for example: Windows, Unix, Database, Network, Monitoring). You can use the host group hierarchy however you choose: some implementations are based on locations while others are based on priority (production, test, development).
When Opsview sets up notifications, you will receive the relevant host alerts for the services you have access to. If you do not want host notifications, you can disable them at the contact’s notification profile.
Note
A contact must have at least 1 service on a host to be within the subset. This means that selecting All host groups, but only, say, the Database Service Group, would mean that a Contact can see only Hosts with database services. Hosts without any database services would not be in this subset.
Troubleshooting Copied
All my administrators do not have CONFIGURESAVE
Copied
If you have locked out all administrators by removing CONFIGURESAVE, you can add it back to your role by running the following in the opsview database:
mysql> insert into roles_access values (10,13);
This will add CONFIGURESAVE to the ‘Administrator’ role (whose id is usually 10).