Azure
Overview
The Azure plugin is a Collection Agent plugin that is used to monitor Azure resources. This plugin collects Azure Monitor metrics using a combination of API calls using the Azure Java SDK and REST API, then it displays data as dataview in Geneos.
In addition, the Azure plugin allows you to:
- Combine metrics from Azure with on-premise, multi-cloud, and hybrid environments for end-to-end visibility.
- Monitor real-time alerts using rule and alert capabilities.
- Minimise cost by using a single enterprise tool for monitoring.
Deployment recommendations
There are multiple approaches in optimising the Azure plugin to monitor a specific estate. In cases where you are nearing the Azure API limits, which is 12000 per hour, you should apply filtering to only monitor the selected services, or deploy other options to run the Azure plugin.
Caution
Since the Azure plugin works by calling into the Azure API, you should be aware of the API usage limits. If the API limits are frequently reached, you may want to limit or monitor the metrics collected, see Azure Monitor API count monitoring. Alternatively, you can also increase the collection interval time. For more information about API limits, see Request limits in Azure.
Deploy Azure through the Azure Marketplace
Use the Deploy Azure MonitorThis through the Azure Marketplace deployment option for the following reasons:
- An easier way for you to deploy the Azure plugin through the Azure Marketplace with built-in dynamic entity mapping to minimise Gateway configuration.
- This deployment support different scenarios to set up the plugin with minimal configuration.
Configure Geneos to deploy Azure plugin
Use the Configure Geneos to deploy Azure Monitor deployment option in the following cases:
- When you require a native deployment option where you configure the Gateway and Netprobe in Geneos on your local machine.
Configure the Azure Event Hub plugin
Azure Event Hub deployment
Azure plugin supports the ability to consume real-time metrics from the Azure Event Hub service. This is an alternative to polling Azure Monitor API, enabling Geneos to monitor your Azure cloud environment at scale and in real-time.
Use the Azure Event Hub deployment option in the following cases:
- If you have Azure diagnostics set up to publish metrics to an Event Hub, you may want to use the Azure Event Hub plugin for gathering metrics. This provides a higher throughput of metrics and is one way to avoid issues caused by Azure API limitations.
- Your Azure Monitor API usage is near the hourly API limit as your Azure estate grows larger. The best approach to preventing this is identifying the priority of services and resources that you want to monitor, and then slowly migrating them to Event Hub streaming to use the Azure Event Hub plugin.
Prerequisites
Geneos environment
The latest version of the Azure Collection Agent plugin requires the following versions of Geneos components:
- Gateway and Netprobe 5.10.x or higher. The same version must be used for the schema.
- Collection Agent 2.x. To run , see setup.
The Azure binaries are packaged with Netprobe, and are stored in the collection_agent folder. Alternatively, you can download separate binaries for the Azure plugin from ITRS Downloads.
Azure environment
The Azure plugin requires the following parameters in order to connect to Azure Monitor:
- Client ID
- Client Secret
- Tenant ID
- Subscriptions ID
The Azure plugin requires an app user to be created which will be used to interface with Azure. In addition, you must configure the appropriate roles to enable access to particular services. Please see the following external documentation:
- Quickstart: Register an application with the Microsoft identity platform
- Assign Azure roles using the Azure portal
The Monitoring Reader built-in role has been tested with the plugin and can be used as a base for creating custom roles.
Deploy Azure through the Azure Marketplace
You can deploy the ITRS’s pre-configured virtual machine through the Azure Marketplace that has a running Netprobe with the Azure plugin on port 7036, and optionally, you can run the Gateway on port 7039 that connects to the probe.
The pre-configured virtual machine image created by ITRS contains configuration files and scripts, see Packaged configuration files.
Note
The default behaviour of deploying the virtual machine through the Azure Marketplace does not require any certificates to enable encrypted communication. If you want to switch to secure encrypted communication, see Run Gateway with secure encrypted communication.
Create a virtual machine in Azure Marketplace
Ensure that your Azure account has the necessary credentials in order to access the application. See the requirements for Azure environment.
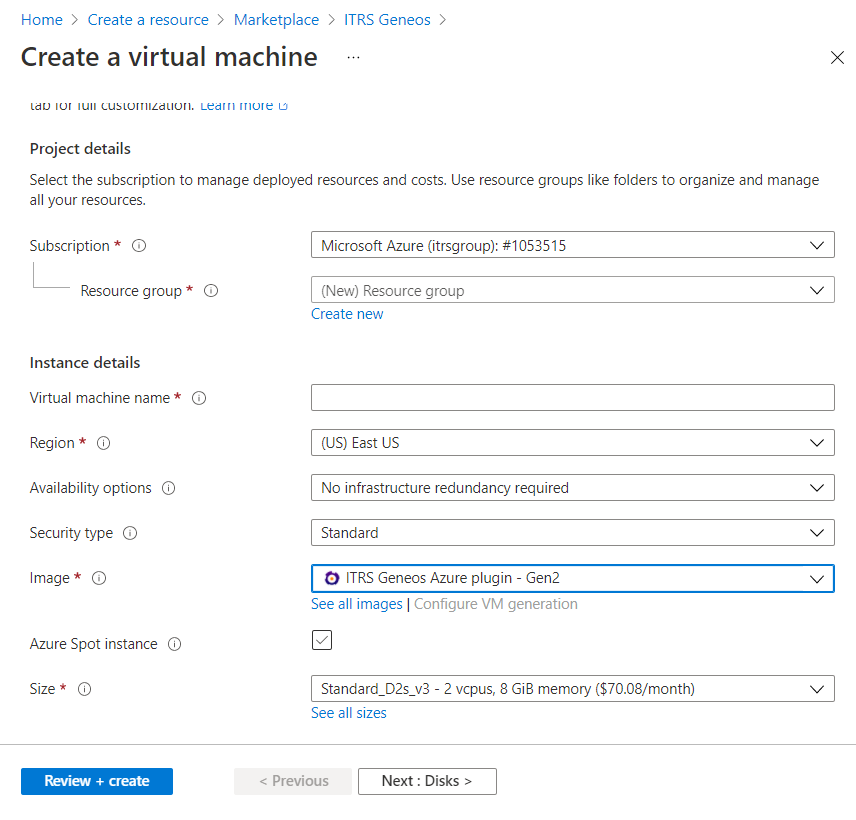
To create a virtual machine in the Azure Marketplace:
-
Open Azure Portal
-
Click Create a resource under Azure services
-
Search for ITRS Geneos, then click Create. This opens the Create a virtual machine page
-
Provide the required information in all tabs under the Create a virtual machine screen. Some fields are mandatory and the value must not be empty
Note
You can configure the remaining required fields depending on your machine requirements. For example, you can freely adjust the size of your virtual machine accordingly and create your own resource group. We only require you to follow the settings below when configuring your virtual machine.- In the Basics tab, ensure that the Image field is set to ITRS Geneos Azure plugin - Gen2.
- In the Advanced tab, add the script below in the Custom data field. This will run the Gateway in demo mode. For other deployment scenarios, you can refer to the Supported scenarios for deploying your virtual machine.
#cloud-config runcmd: - bash /geneos/set-azure-parameters.sh --clientID <"client-id"> --clientSecret <"client-secret"> --tenantID <"tenant-id"> --subsID <"subscription-id"> --gatewayArgs "-demo"In this example, the virtual machine will run the Collection Agent, Netprobe, and Gateway because the
--gatewayArgs "-demo"was used in the parameters script. The Gateway will run in demo mode that does not require licencing and with minimal configuration needed. -
Once the configuration for the virtual machine is completed, click Review + create.
- If you select SSH public key on the Basics tab as the authentication type, Azure will ask you to download private key.
- Azure will validate all the requirements that you submitted to create a virtual machine.
- Click Create.
-
Wait until the deployment status is completed. Then, you can open your resource.
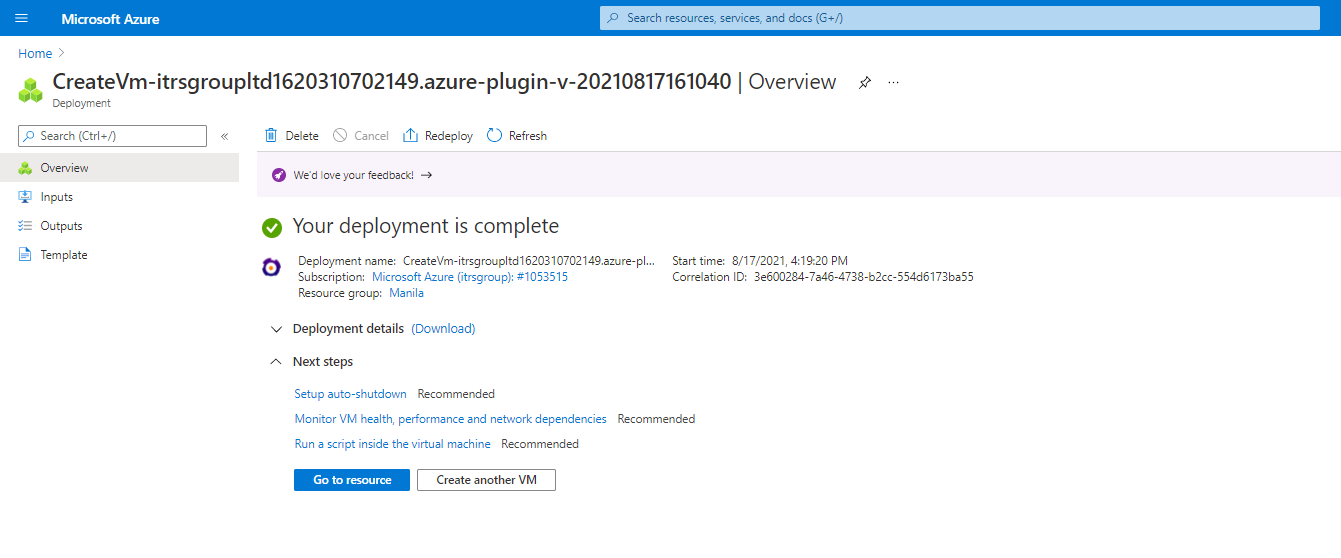
- After the virtual machine is created, go to the resource and add the inbound port rules for port
7036.- In the Networking > Add inbound port rule for
7036, change the Destination port ranges to7036. - In Protocol > TCP, update the name.
- In the Networking > Add inbound port rule for
7039, change the Destination port ranges to7039. - In Protocol > TCP, update the name.
- In the Networking > Add inbound port rule for
- Add the inbound port rules for port
7039.- In the Networking > Add inbound port rule for
7039, change the Destination port ranges to7039. - In Protocol > TCP, update the name.
- In the Networking > Add inbound port rule for
- Navigate to Overview, copy the public IP address provided to connect via SSH client.
- Open Active Console Settings > Connections.
- In the Connections section, add the hostname or the public IP address of your virtual machine.
- Click OK. This displays the monitored Azure metrics and the Azure Monitor API count monitoring. See Example dataview.
Note
Once you successfully create your virtual machine, and connect Gateway from the Active Console, check if the monitored Azure resources display in the dataview. If not, then you should check the status of the Gateway and Netprobe in the virtual machine, see Check the Gateway and Netprobe status.
Supported scenarios for deploying your virtual machine
This section provides you a list of scenarios to deploy the Azure plugin through the Azure Marketplace. If you want to update your virtual machine, see Update virtual machine using parameters.
Run Gateway with secure encrypted communication
You can run a secured Netprobe in the virtual machine by retrieving these files from a key vault:
Note
You can only run a secured Netprobe or Gateway after creating a virtual machine. Then, you must move the certificate files below to your virtual machine.
- SSL certificate
- SSL certificate key
- SSL certificate chain
You should manually configure the inbound port in the following cases:
- When you enable a secured Gateway, add the port that you set in
gateway.setup.xmlof your virtual machine which is a secured port. - When you add the
-portin--netprobeArgs, add the inbound port that you set in-port. - When you add the
-portin--gatewayArgs, add the inbound port that you set in-port.
To configure the inbound port, navigate to your virtual machine in Azure Portal, then click Settings > Networking.
To view the parameters that you can use in the --netprobeArgs parameter, see –netprobeArgs, and for --gatewayArgs, see –gatewayArgs.
Run this script in your virtual machine:
bash /geneos/set-azure-parameters.sh --gatewayArgs "-licd-host <host> -licd-port <port> -ssl-certificate <file> -ssl-certificate-key <file> -ssl-certificate-chain <file>" --netprobeArgs "-secure -ssl-certificate <file> -ssl-certificate-key <file> -ssl-certificate-chain <file>"
Run Gateway connecting to an existing Licence Daemon
In this mode, the virtual machine will run the Collection Agent, Netprobe, and Gateway. The Gateway must be connected to an existing LICD that requires normal licencing. Then, you can connect Active Console to the Gateway using the public IP address of your virtual machine on port 7039.
Run this script in your virtual machine:
bash /geneos/set-azure-parameters.sh --clientID <"client-id"> --clientSecret <"client-secret"> --tenantID <"tenant-id"> --subsID <"subscription-id"> --gatewayArgs "-licd-host <hostname> -licd-port <port>"
The Gateway in the virtual machine will use its default values, a port on 7039, and LICD localhost on 7041 if none are provided.
Note
When the default values are not used, for example, if--gatewayArgs "-licd-port 7040"is run, you must create your own Gateway setup and configure the inbound port to allow connection through port7040in your Azure virtual machine.
Run Self-announcing Netprobe connecting to an existing Gateway
In this mode, the virtual machine will run the Collection Agent and Netprobe as a Self-announcing Netprobe. The SAN probes need to connect to your own Gateway.
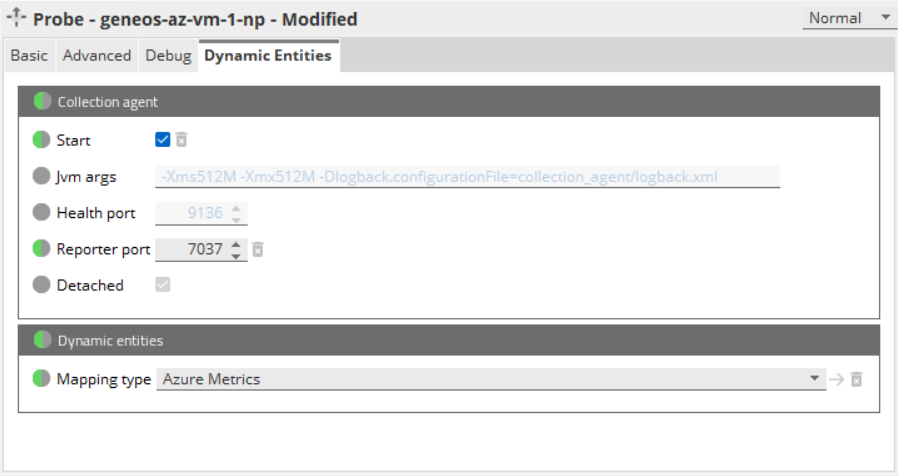
You must add the mapping type named Azure Metrics to your Gateway to see the data in your Active Console. For guidance on how to add the mapping type, refer to the steps in Configure Geneos to deploy Azure Monitor.
Run this script in your virtual machine:
bash /geneos/set-azure-parameters.sh --clientID <"client-id"> --clientSecret <"client-secret"> --tenantID <"tenant-id"> --subsID <"subscription-id"> --san "gwHost=<host>;gwPort=<port>;gwSecure=<value>"
When --san is enabled, you should not use the -setup option in the --netprobeArgs parameter. If you use the -setup option, this will be ignored.
Run normal Netprobe connecting to an existing Gateway
In this mode, the virtual machine will run the Collection Agent and Netprobe in normal mode. This requires you to configure the Gateway to connect to the Netprobe on port 7036.
You must add the mapping type named Azure Metrics to your Gateway to see the data in the Active Console. For guidance on how to add the mapping type, refer to the steps in Configure Geneos to deploy Azure Monitor.
Run this script in your virtual machine:
bash /geneos/set-azure-parameters.sh --clientID <"client-id"> --clientSecret <"client-secret"> --tenantID <"tenant-id"> --subsID <"subscription-id">
Update virtual machine using parameters
You can test or update your newly created virtual machine in the . To do this, you can use the supported arguments to the set-azure-parameters.sh script.
- Open your virtual machine under Recent resources.
- Click Run command > RunShellScript. This opens the Run Command Script screen.
- Update the script in the Linux Shell Script field. Then, click Run.
Here is the list of parameters that you can use for the set-azure-parameters.sh configuration:
| Option | Description |
|---|---|
--clientID
|
Azure client ID to be used by the Netprobe. Mandatory: Yes |
--clientSecret
|
Azure client secret associated with the client ID. Mandatory: Yes |
--subsID
|
Subscription ID associated with an Azure subscription. Mandatory: Yes |
--tenantID
|
Tenant ID associated with the Azure Active Directory. Mandatory: Yes |
--gatewayArgs
|
Starts the Gateway installed in the virtual machine using the command line options provided. Example:
Note: Demo mode has the following limitations. For more information, see Demo mode in Gateway Licensing. Also, when switching between secure and insecure Gateway, you must delete the following files in the Gateway directory in your virtual machine: cache folder and |
--netprobeArgs |
Starts the Netprobe installed in the virtual machine using the command line options provided. Example: Options:
|
--loggerLevel
|
Sets the logger level of the plugin. Possible values: Mandatory: No Default value: |
--enabledResources
|
Comma-separated list of Azure resource types that will be monitored. Sample usage: Mandatory: No Default value: |
--collectionInterval
|
Interval (in milliseconds) between publications. Mandatory: No Default value: |
--delay
|
Adds delay (in minutes) before retrieving the Azure metrics. This is useful to allow Azure time to complete generation of metric values before they are collected by the plugin. Mandatory: No Default value: |
--san
|
Runs the Netprobe as a Self-announcing Netprobe. The options are defined by adding key-value pairs separated semicolon.
Sample usage: Options:
When no option is defined, the probe will run as a Self-announcing Netprobe using the current values defined.
|
-h | --help |
Shows the help text. |
- The client ID, client secret, subscription ID, and tenant ID must all be provided when updating credentials for the Azure plugin.
- To update your logger level, list of enabled resources, collection interval, or SAN options without updating the Azure credentials, you can run any of the following in the Run command > RunShellScript:
bash set-azure-parameters.sh --enabledResources <resources>
bash set-azure-parameters.sh --loggerLevel <logger-level>
bash set-azure-parameters.sh --collectionInterval <interval>
bash set-azure-parameters.sh --san
bash set-azure-parameters.sh --san <san-options>
bash set-azure-parameters.sh --enabledResources <resources> --loggerLevel <logger-level> --collectionInterval <interval> --san <san-options>
- Setting the
collection-intervalto a smaller value could cause the plugin to reach the throttling limit more frequently. For more information about throttling requests, see Request limits in Azure. - If no parameter is provided, the shell script will exit.
Packaged configuration files
The pre-configured virtual machine image created by contains the following:
-
Gateway, Netprobe, Collection Agent, and Azure plugin inside
/geneoswith the following configuration files:collection-agent.ymlis modified to call on variables set from shell script.gateway.setup.xmlis pre-configured to automatically connect the to the in the virtual machine.logback.xmlis modified to allow log rollover.san.xmlfor running the as .
-
Helper scripts:
/geneos/get-diagnostics.sh/geneos/set-azure-parameters.sh/geneos/set-logger-info.sh/geneos/add-enabled-resources.py/geneos/update-collection-interval.py/geneos/update-delay.py
-
Service files:
/usr/bin/start-netprobe.sh/usr/bin/start-gateway.sh/lib/systemd/system/netprobe.service/lib/systemd/system/gateway.service
Troubleshooting
Check the Gateway and Netprobe status
You can run the following commands to check the state of the Gateway and Netprobe in your virtual machine.
Note
Both the Gateway and Netprobe on the virtual machine are run as asystemdservice.
- Open a terminal session in your virtual machine and connect to SSH.
- Run this command to check if the Gateway and Netprobe are running in the virtual machine:
# Check the status of Netprobe systemctl status netprobe # Check the status of Gateway systemctl status gateway - Run this command to restart the Gateway and Netprobe if they fail during the initialisation of the virtual machine:
# Restart the Netprobe systemctl restart netprobe # Restart the Gateway systemctl restart gateway
Get the diagnostic files
For troubleshooting purposes, you can download a diagnostic file from the Azure virtual machine storage account with the following contents:
- Collection Agent
- Collection Agent logs
- Netprobe logs
To set up your Storage account:
-
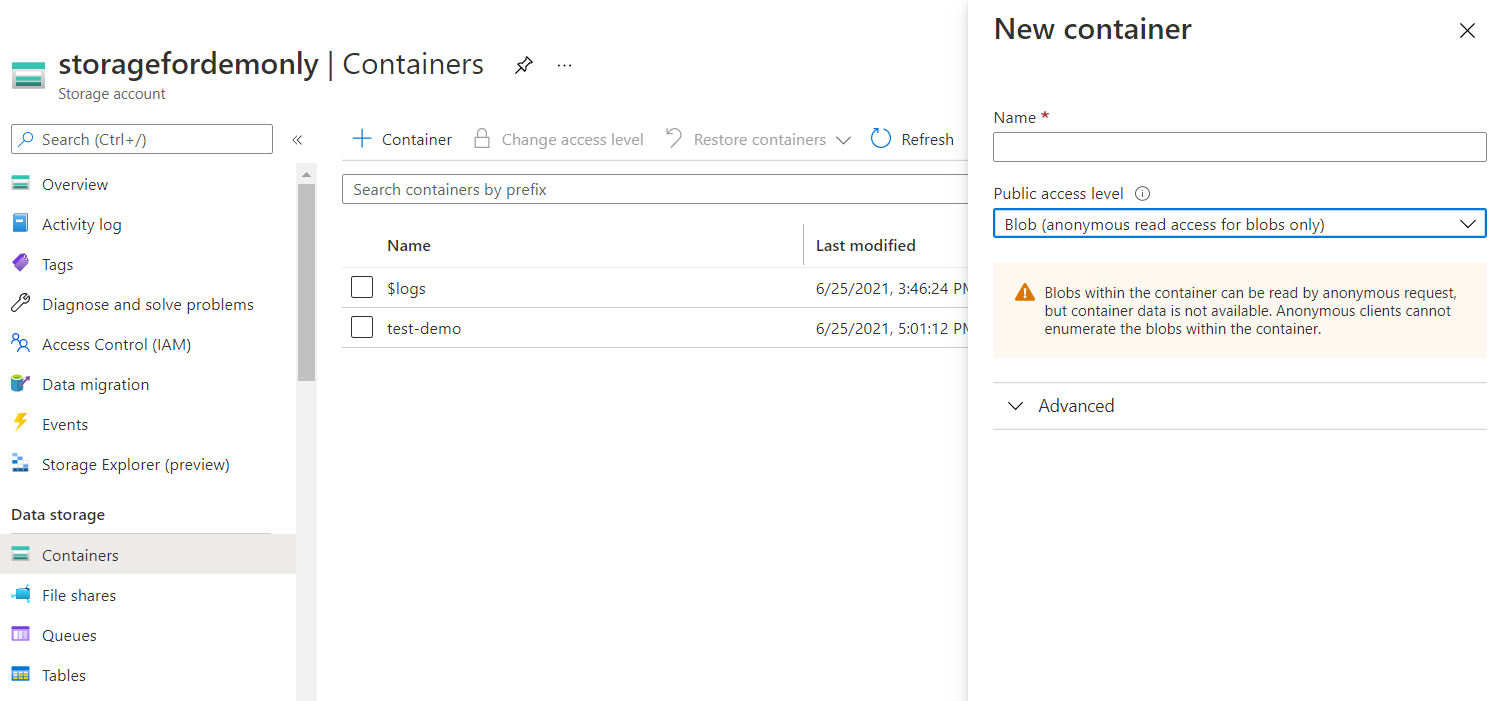
Navigate to the Azure Portal
-
Click Storage Accounts under the Azure services.
-
Search for your storage account. If you have not created a storage account, click Create.
-
Enter a name for your container, and set the Public access level to Blob. Then, click Create.
-
Once the container is created, click Shared access tokens under Settings, and then provide the following information:
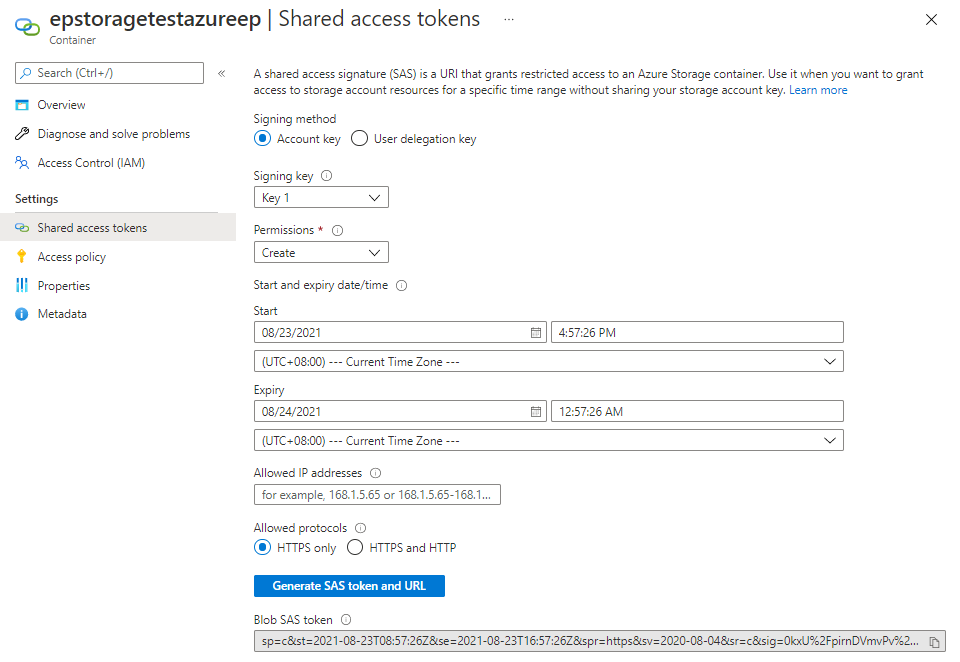
- Under Signing method, select the Account key button.
- On the Permissions menu, select Create.
- Set the Start and Expiry date and time.
- Set the allowed IP addresses, if necessary.
- Under Allowed protocols, select the HTTPS only button.
-
Click Generate SAS token and URL, then copy the Blob SAS token.
-
In your container, go to Settings > Properties, then copy the URL which is needed for the storage account container URL.
-
Navigate to the Azure Portal, and open your virtual machine.
- Go to the Operations > Run command > RunShellScript. This opens the Run Command Script screen.
- Enter the following in the Linux Shell Script field:
bash /geneos/get-diagnostics.sh --url "<Azure storage account container URL>" --token "<Blob SAS token>" -
Once successful, your diagnostics file will be stored in the Storage container > Storage Explorer with a filename
netprobe-logs-<timestamp>.tar.gz.
Configure Geneos to deploy Azure
The Azure plugin supports Collection Agent publication into Geneos using dynamic managed entities. Setting up this plugin in Geneos involves three primary steps:
- Configure the Collection Agent YAML file and provide the required settings for your Azure account.
- Set the mappings in the Gateway.
- Enable dynamic managed entities. Alternatively, you can use Self-announcing Netprobes to enable dynamic entities. See Self-announcing Netprobes in Collection Agent setup.
To set up the Azure plugin in Geneos:
- You must edit the
collection-agent.ymlfile on your local machine where the binaries are stored either by:
- Indicating the required settings for client ID, client secret, tenant ID, and subscription ID in the YAML file.
- Indicating the required settings as environment variables as shown in the example configuration below. See User Variables and Environments.
| Setting | Description |
|---|---|
enabled-resources
|
To add more Azure resources to monitor, you can add them in enabled-resources following this format: <resource.provider>/<resource-type>. This setting allows you to filter based on the resource type. Without this setting, the Azure plugin will pick up metrics for all available Azure services. See Monitored Azure services. |
published-tags
|
This is useful if you want to use a tag in the dynamic entities mapping configuration. If this is not set, no tags will be included in the metrics published. |
resource-group-filter
|
If a resource does not have a tag that is listed in the configuration, then the property will not be included in the metrics published. |
tag-filter
|
Allows you to monitor only certain resources with tags that match what is configured. A resource will be monitored only if all tags match the resource, for example, the tag is present and the tag value matches the regex provided. |
- Set the mappings in the Gateway. Follow the procedures in Create Dynamic Entities in Collection Agent setup. Then, select Azure Monitor V2 in the Built in > Name section.
- Link the mapping type to the recently created Azure mapping.
- Enable dynamic managed entities. For reference, see Add a Mapping type in Dynamic Entities.
collectors:
- name: azure
type: plugin
class-name: AzureMonitorCollector
# Interval (in millis) between publications (optional, defaults to five minutes)
collection-interval: 300000
# The Azure client id that can be used for this application (required)
client-id: ${env:CLIENT_ID}
# The Azure secret associated with the client id (required)
client-secret: ${env:CLIENT_SECRET}
# The Azure tenant id to be monitored (required)
tenant-id: ${env:TENANT_ID}
# The Azure subscription id to be used for monitoring (required)
subscription-id: ${env:SUBSCRIPTION_ID}
# Filter resources by resource group name according to the provided Java regex
resource-group-filter: (UAT-group)|(PROD-group)
# Specify a list of key or value pairs which correspond to Azure resource tags and values
tag-filter:
Dev: (Name 1)|(Name 2)
Owner: .*
# Specify a list of tags which will be published as a datapoint property
published-tags:
- Environment
- Purpose
# Lists the resource type(s) that will be monitored (optional, defaults to listing all available resource types)
enabled-resources:
- Microsoft.Compute/disks
- Microsoft.Network/azureFirewalls
Note
To check if there are any errors in the mapping, you can set up the Dynamic Entities Health, check Azure Monitor API count monitoring, or look at the Collection Agent log file.
Example dataview
Once you set up the plugin and mappings successfully, the monitored Azure services including their metrics will display in a dataview in Geneos. In the example below, the Azure resources are sorted according to resource_provider as an entity, resource_type as a sampler, and resource_group as a dataview.
For detailed information about Azure services, see Services Monitored > Azure Monitor Metrics.
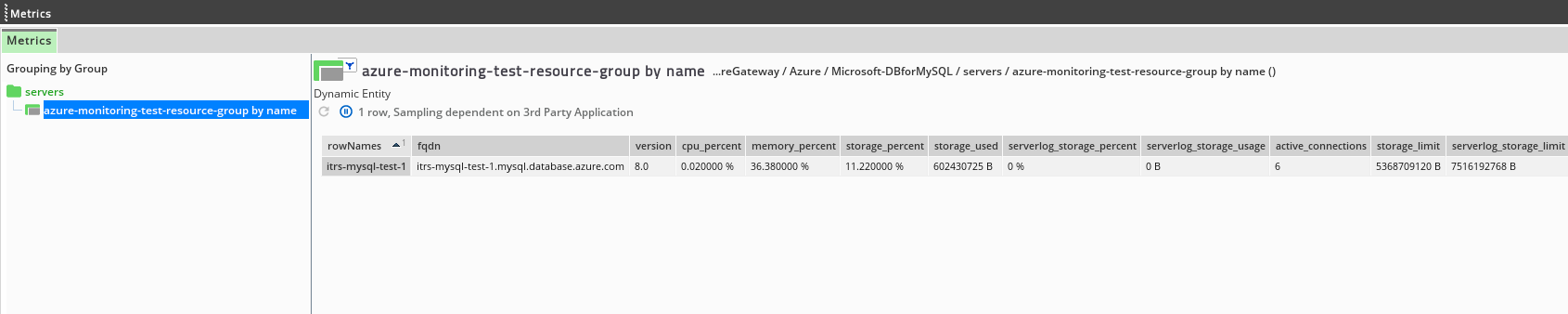
To define how items in the Geneos tree structure are generated from the labels of a datapoint, see Geneos items in Dynamic Entities.
Custom mappings
Alternatively, the Azure plugin also allows you to create custom mappings so you can modify the display of information in the Geneos dataview.
The mappings can be configured differently by using available dimensions or properties. All metrics published by the Azure plugin have a data_kind of azure_v1.
To create custom mappings:
- Navigate to your Azure mapping in Dynamic entities > Mappings.
- In Options, selection custom.
- In the Geneos items > Label, enter the following:
resource_groupas an entityresource_providerandresource_typeas a sampler
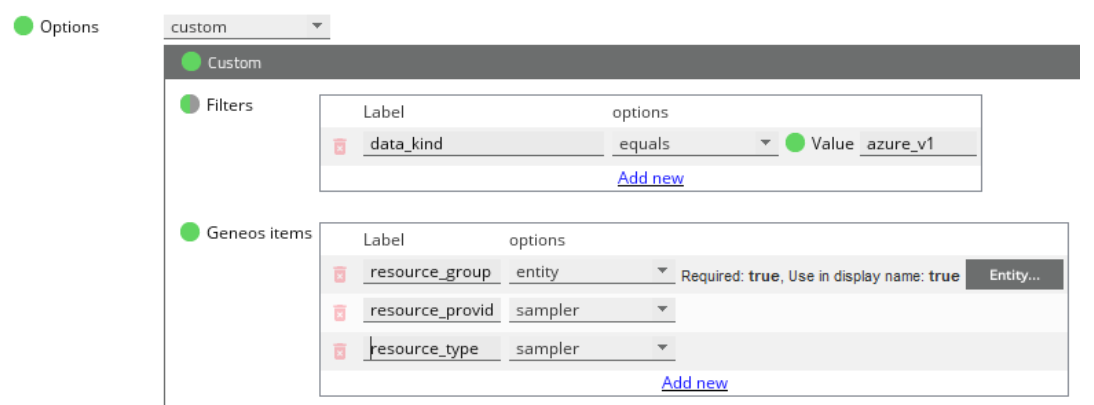
The following metrics dimension or properties can be used to map or filter resources in a custom mapping.
| Metric property | Description |
|---|---|
resource_provider
|
Resource provider values for each service that can be found in Azure monitor services. The builtIn mapping uses this to group similar resource types in an entity. |
resource_type
|
Resource type values for each service that can be found in Azure monitor services. The builtIn mapping uses this to group similar resource types in an entity. |
resource_group
|
Corresponds to the resource's resource group. The builtIn mapping uses this as the dataview name. |
region
|
Region where the resource is in. |
name
|
Name of the resource. |
Further, the Azure tags for resources will be transferred to metrics which is useful if the Azure estate has its own way of organising resources by tags.
You can also use Show Dynamic Mappings on the metrics to see the dimensions or properties that can be used for the mapping.
The Azure tags will become a property that can be seen in Show Dynamic Mappings. Additionally, there are several Azure plugin built-in properties:
| Azure built-in property | Description |
|---|---|
| Azure Tag |
Key-value pair that will be a label-value pair in the dynamic mapping. For example, the Azure tag |
aggregation_type
|
Default aggregation type for a specific metric. |
region
|
Location where the resource resides when deployed in Azure. |
Note
Given the nature of the Azure tag having different variations of key-value pairs (depending on how you set this up), when a tag’s key clashes with an existing property, the tag will not override the existing property. For example, if you create a tagdata_kind=test, this will not override the built-in propertydata_kind.
Monitored Azure services
The Azure plugin fetches available metrics for Azure resources. The following limitations apply:
- Aggregations are performed using the smallest time grain supported by each metric.
- Only the default aggregation is used for each metric available.
- Some metrics may not be immediately available, which is the expected behaviour of Azure Monitor. Some metrics may be available for premium resources only, or some may be awaiting actions from the user or system to be done on the resource, for example, pulling a docker image from a container registry makes the
SuccessfulPullCountandTotalPullCountmetrics available. - The Azure plugin will gather as many metrics as possible for each collection interval. Data already reported from previous collection intervals or timestamp will no longer be gathered.
For more information, refer to the individual Azure resource documentation listed under Services Monitored > Azure Monitor Metrics.
Caution
Since the Azure plugin works by calling into the Azure API, you should be aware of the API usage limits. If the API limits are frequently reached, you may want to limit or monitor the metrics collected, see Azure Monitor API count monitoring. Alternatively, you can also increase the collection interval time. For more information about API limits, see Request limits in Azure.
The table below lists the Azure Monitor services that this plugin can monitor. Each service has its own set of metrics that can be displayed as data in Geneos dataview.
For detailed information about Azure services, see Services Monitored > Azure Monitor Metrics.
| Azure service | Resource provider | Resource type |
|---|---|---|
| API Management Service | Microsoft.ApiManagement
|
service
|
| App Service Plans | Microsoft.Web
|
serverfarms
|
| App Services | Microsoft.Web
|
sites
|
| Application Gateways | Microsoft.Network
|
applicationGateways
|
| Application Insights | Microsoft.Insights
|
components
|
| Automation Accounts | Microsoft.Automation
|
automationAccounts
|
| Batch Accounts | Microsoft.Batch
|
batchAccounts
|
| Cognitive Services | Microsoft.CognitiveServices
|
accounts
|
| Container Groups | Microsoft.ContainerInstance
|
containerGroups
|
| Container Registries | Microsoft.ContainerRegistry
|
registries
|
| Cosmos DB accounts | Microsoft.DocumentDB
|
databaseAccounts
|
| Disks | Microsoft.Compute
|
disks
|
| DNS Zones | Microsoft.Network
|
dnszones
|
| Event Hub Namepsace | Microsoft.EventHub
|
namespaces
|
| Express Route Circuits | Microsoft.Network
|
expressRouteCircuits
|
| Firewalls | Microsoft.Network
|
azureFirewalls
|
| Front Doors | Microsoft.Network
|
frontdoors
|
| Function Apps | Microsoft.Web
|
sites
|
| Key Vaults | Microsoft.KeyVault
|
vaults
|
| Load Balancers | Microsoft.Network
|
loadBalancers
|
| Local/Virtual Network Gateway Connections | Microsoft.Network
|
connections
|
| MariaDB Servers | Microsoft.DBforMariaDB
|
servers
|
| MySQL Servers | Microsoft.DBforMySQL
|
servers
|
| Network Interfaces | Microsoft.Network
|
networkInterfaces
|
| Network Watchers/Connection Monitors | Microsoft.Network
|
networkWatchers
|
| Azure Servers | Microsoft.DBforPostgreSQL
|
servers
|
| Search Services | Microsoft.Search
|
searchServices
|
| Service Bus Namespace | Microsoft.ServiceBus
|
namespaces
|
| SQL Server/Databases | Microsoft.Sql
|
servers
|
| SQL Server/Elastic Pools | Microsoft.Sql
|
servers
|
| Storage Accounts | Microsoft.Storage
|
storageAccounts
|
| Traffic Manager Profiles | Microsoft.Network
|
trafficManagerProfiles
|
| Virtual Machine Scale Sets | Microsoft.Compute
|
virtualMachineScaleSets
|
| Virtual Machine Scale Sets/Virtual Machines | Microsoft.Compute
|
virtualMachineScaleSets
|
| Virtual Machines | Microsoft.Compute
|
virtualMachines
|
| Virtual Network Gateways | Microsoft.Network
|
virtualNetworkGateways
|
| Virtual Networks | Microsoft.Network
|
virtualNetworks
|
Additional attributes
In addition to the attributes of metrics that Azure Monitor provides, this plugin also collects the following information for each resource.
| Azure service | Attribute | Attribute description |
|---|---|---|
| API Management Services | sku_capacity
|
Capacity of the SKU or the number of deployed units of the SKU. |
| API Management Services | sku_name
|
Name of the API Management Service SKU. |
| App Service Plans | capacity
|
Capacity of the App Service Plan. |
| App Service Plans | max_instances
|
Maximum number of instances that can be assigned to the App Service Plan. |
| App Service Plans | number_of_web_apps
|
Number of web apps assigned to the App Service Plan. |
| App Service Plans | operating_system
|
Operating system where the app is running on. |
| App Services | default_hostname
|
Default hostname of the app. |
| App Services | state
|
State of the app. |
| App Services | app_service_plan
|
Name of the app's App Service Plan. |
| Application Gateways | operational_state
|
Operational state of the application gateway. |
| Application Insights | app_id
|
Application Insights Unique ID of the application. |
| Application Insights | app_type
|
Type of application being monitored. |
| Application Insights | provisioning_state
|
State of the app whether it has been provisioned within its defined resource group. |
| Application Insights | sampling_percentage
|
Percentage of the data produced by the application being monitored that is being sampled for Application Insights telemetry. |
| Automation Account | creation_time
|
Account creation date. |
| Automation Account | last_modified_time
|
Account last modified date. |
| Batch Accounts | account_endpoint
|
Batch account endpoint. |
| Cognitive Services | endpoint
|
Endpoint of the created Azure Cognitive Services account. |
| Cognitive Services | kind
|
Resource kind. |
| Cognitive Services | public_network_access
|
States if public endpoint access is allowed. |
| Cognitive Services | sku_name
|
SKU Name of an Azure Cognitive Services account. |
| Cognitive Services | sku_tier
|
SKU Tier of an Azure Cognitive Services account. |
| Container Groups | state
|
State of the container group. |
| Container Groups | os_type
|
Base level OS type required by the containers in the group. |
| Container Groups | ip_address
|
IP address. |
| Container Registries | login_server_url
|
URL that can be used to log into the container registry. |
| Cosmos DB accounts | document_endpoint
|
Connection endpoint for the Cosmos DB database account. |
| DB For MariaDB | fqdn
|
Fully Qualified Domain Name. |
| DB For MariaDB | version
|
MariaDB version. |
| DB For MySQL | fqdn
|
Fully Qualified Domain Name. |
| DB For MySQL | version
|
MySQL version. |
| DB For Postgresql | fqdn
|
Fully Qualified Domain Name. |
| DB For Postgresql | version
|
Postgresql version. |
| Disks | vm_id
|
Resource ID of the virtual machine the disk is attached to. |
| DNS Zones | zone_type
|
DNS Zone type. |
| DNS Zones | record_sets_count
|
Current number of record sets in the DNS zone. |
| DNS Zones | record_sets_max_count
|
Maximum number of record sets that can be created in the DNS zone. |
| Event Hub Namespaces | service_bus_endpoint
|
Service bus endpoint associated with the namespace. |
| Express Route Circuits | circuit_provisioning_state
|
CircuitProvisioningState state of the resource. |
| Firewalls | provisioning_state
|
Provisioning state of the Azure firewall resource. |
| Firewalls | sku_name
|
Name of the Azure Firewall SKU. |
| Firewalls | sku_tier
|
Tier of the Azure Firewall SKU. |
| Firewalls | threat_intel_mode
|
Operation mode for Threat Intelligence. |
| Frontdoors | cName
|
The host that each frontendEndpoint must CNAME to. |
| Function Apps | default_hostname
|
Default hostname of the app |
| Function Apps | state
|
State of the function app. |
| Function Apps | app_service_plan
|
Name of the app's App Service Plan. |
| Key Vaults | N/A | |
| Load balancers | N/A | |
| Local network Gateways/Connections | network_gateway1
|
Name of the virtual network gateway. |
| Local network Gateways/Connections | network_gateway2
|
Name of the local network gateway. |
| Network interfaces | vm_id
|
Resource ID of the virtual machine the network interface is associated with. |
| Network interfaces | public_ip_*
|
Public IP address the network interface is associated with. |
| Network Watchers | connection_monitor_count
|
Current number of connection monitors in the network watcher. |
| Network Watchers/Connection Monitors | interval_in_secs
|
Monitoring interval in seconds. |
| Network Watchers/Connection Monitors | status
|
Monitoring status of the connection monitor. |
| Search Services | status
|
Status of the search service. |
| Service Bus Namespace | price_tier
|
Price tier of the service bus. |
| Service Bus Queue | status
|
Status of the Queue under a given service. |
| Service Bus Topic | status
|
Status of the Topic under a given service bus. |
| SQL Server | state
|
State of the SQL Server. |
| SQL Server/Database | elastic_pool
|
Name of elastic pool associated with the SQL database. |
| SQL Server/Elastic Pools | state
|
State of the elastic pool. |
| Storage accounts | primary_endpoint_blob
|
Primary blob endpoint of the storage account. |
| Storage accounts | primary_endpoint_file
|
Primary file endpoint of the storage account. |
| Storage accounts | primary_endpoint_queue
|
Primary queue endpoint of the storage account. |
| Storage accounts | primary_endpoint_table
|
Primary table endpoint of the storage account. |
| Storage accounts | primary_endpoint_dfs
|
Primary dfs endpoint of the storage account. |
| Storage accounts | primary_endpoint_web
|
Primary web endpoint of the storage account. |
| Traffic Manager Profiles | N/A | |
| Virtual Machine Scale Sets | instances
|
Number of virtual machine instances in the scale set. |
| Virtual Machine Scale Sets/Virtual Machines | power_state
|
Power state of the virtual machine instance. |
| Virtual Machine Scale Sets/Virtual Machines | computer_name
|
Computer name of the virtual machine instance. |
| Virtual Machine Scale Sets/Virtual Machines | os_type
|
Operating system of this virtual machine. |
| Virtual Machines | os_type
|
Operating system of this virtual machine. |
| Virtual Network Gateways | gateway_type
|
Virtual Network Gateway type. |
| Virtual Network Gateways | sku_name
|
SKU name of the Virtual network gateway. |
| Virtual Network Gateways | sku_tier
|
SKU tier of the Virtual network gateway. |
| Virtual Network Gateways/Connections | network_gateway1
|
Name of the first virtual network gateway. |
| Virtual Network Gateways/Connections | network_gateway2
|
Name of the second virtual network gateway. |
| Virtual Networks | total_address_spaces
|
Total number of address spaces of the virtual network. |
| Virtual Networks | total_peerings
|
Total number of peering of the virtual network. |
| Virtual Networks | total_subnets
|
Total number of subnets of the virtual network. |
| Virtual Networks | ddos_protection_enabled
|
True if DDoS protection is enabled for all protected resources in the virtual network. |
| Virtual Networks | vm_protection_enabled
|
True if VM protection is enabled for all the subnets in the virtual network. |
Azure API count monitoring
You can also monitor the self monitoring API stats and other metrics of the Azure plugin. This is useful to keep a count of the number of API requests and current monitored resources.
A selfMonitoring managed entity will be available in the Active Console under the ITRS managed entity when you configure correctly the Azure plugin. The selfMonitoring managed entity does not require any further configuration, or parameter to be set in the YAML file.
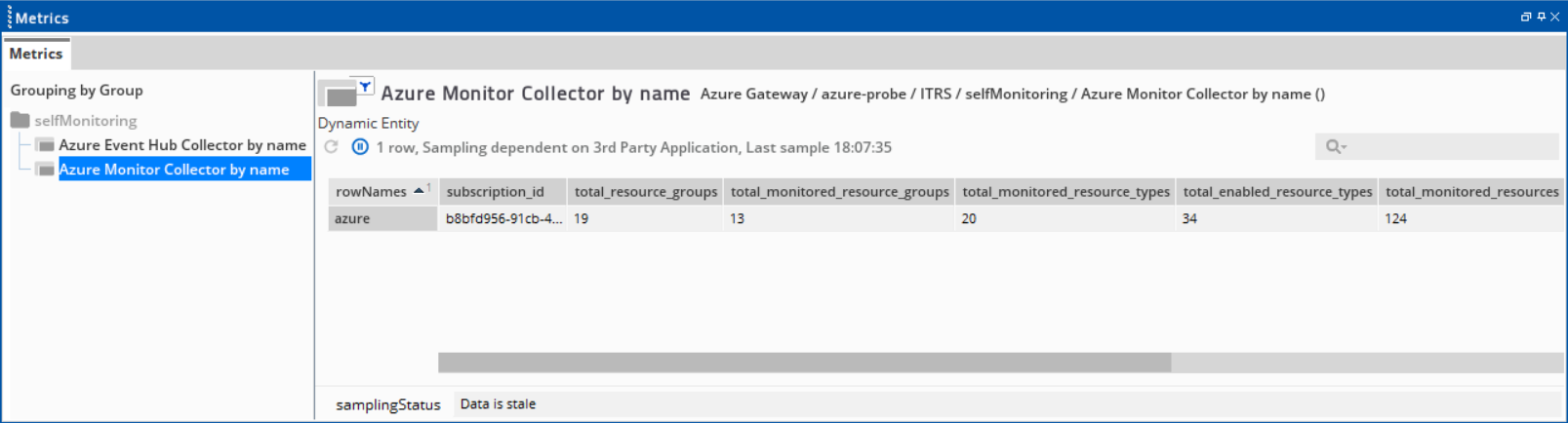
This dataview is created based on these dimensions and their mappings:
resource_group: Azure Monitor Collectorresource_type: selfMonitoringresource_provider: ITRS
The selfMonitoring managed entity displays a dataview that has the following metrics:
| Field | Description |
|---|---|
| rowname | Plugin name indicated in the collection-agent.yml. This follows the format <plugin name - ITRS>. |
| subscription_id | Subscription ID indicated in the collection-agent.yml. |
| total_resource_groups |
Total number of resource groups available on your Azure estate. This resets every collection interval. |
| total_monitored_resource_groups |
Total number of resource groups that match the This resets every collection interval. |
| total_monitored_resource_types | Total number of resource types that the plugin is currently monitoring. |
| total_enabled_resource_types | Total number of resource types listed on enabled-resources parameter in the collection-agent.yml. |
| total_monitored_resources |
Total number of resources Monitored Azure services that have metrics and are displayed on dataviews. This resets every collection interval. |
| collection_interval | Collection interval indicated in the collection-agent.yml. |
| total_api_count_per_collection_interval | Total number of Azure API calls made by Azure Monitor per collection interval. |
| total_api_count_rate_per_hour |
Total number of Azure API calls made by Azure Monitor per hour. |